Online data breaches are common nowadays. Information stored in unhashed (unencrypted) databased is a common site for sloppy backend developers. This means your password is stored as “mysecretpassword123noonewillknow” rather than a generated password that is encrypted with a secret key that will be as this – “v6Mut91BqCw5EPZ74”.
Hackers (maybe a 16 year old in a university dorm room) easily accesses a loophole in a server (maybe due to a vulnerability, a trojan application, a github push mistake with a secret key or worst still.. an easy to guess bruteforce password). There a database can be download with users information including your email and **usual password.
This information is easily sold on blackmarkets or illegally used to commit crimes such as manipulating bank information without your permission.
What can you do?
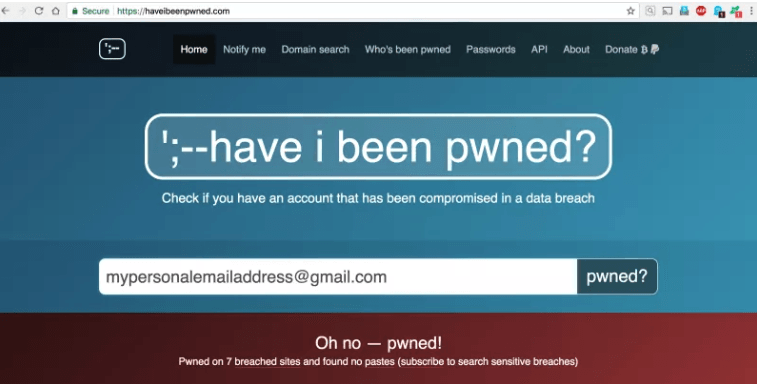
First check if your email is compromised by using public service checkers such as ihavebeenpwnd (https://haveibeenpwned.com/) which checks your email against vulnerabilities and hacked services such as linkedin back in May 2006 (http://fortune.com/2016/05/18/linkedin-data-breach-email-password/)
Secondly, use a password generator such as keeweb or 1password that creates (unique) password for each service you use. Meaning that if your information is stolen on website A… your details wont be compromised on website B.
Finally, rotate your password at least monthly (which is the industry requirement). Also add in 2factor authentication such as adding a mobile phone number to your security options. This will prompt an alert if someone is accessing your account and also request a special random code each time you access the service.
Keep safe and ensure your data is well secured. Even though there are X number of ways hackers can get your information, extra steps taken will ensure you are not an easy target.
Keeping secure and checking if your password is safe?